In this part of the series, I will detail how to request a certificate from your Certificate Authority using the newly created SCOM Template and then I will also explain how to import that certificate into the requesting server's 'Local Computer - Certificate' store.
Requesting a SCOM certificate from a Windows Server 2008 Enterprise CA
Log on to the computer where you want to request a certificate – e.g. RMS, MS, Gateway server or untrusted domain server.
Firstly, you need to ensure that you can ping by using FQDN, the SCOM Management Server from the untrusted domain /DMZ or SCOM Gateway server and then also you must be able to ping the untrusted domain / DMZ or SCOM Gateway server from the SCOM Management Server too. You may need to use static host entries on the local computers to achieve this but it is imperative that this step is complete before moving onto the next steps.
Start Internet Explorer, and connect to the Certificate Enrolment URL on the computer hosting Certificate Services; for example, http://<servername>/certsrv
On the Microsoft Certificate Services Welcome page, click Request a certificate.
On the Request a Certificate page, click Or, submit an advanced certificate request.
On the Advanced Certificate Request page, click Create and submit a request to this CA.
If you are using Windows Server 2008 with Internet Explorer 7 or higher, you will more than likely come across an Active-X error when you get to the next page similar to the one in the screen below
To resolve this issue, open Internet Explorer properties and go to the ‘Security’ tab, then click on ‘Trusted Sites’ and then select the ‘Sites’ button.
Add the http://<servername>/certsrv URL to the ‘Trusted Sites’ Websites list and un-tick ‘Require server verification (https:) for all sites in this zone’ – This step can be omitted if your URL is published on https instead of http however.
Back on the ‘Security’ tab with ‘Trusted Sites’ highlighted, ensure you change the security level to ‘Low’ as the diagram below shows
Now you should be able to browse back to the http://<servername>/certsrv homepage and then once more, click on the ‘Request a Certificate’ link
From the next window, again select the ‘Advanced Certificate Request’ option and then selec the ‘Create and submit a request to this CA’ option from the next window again.
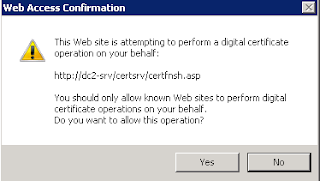
If you see an Active-X error and a Web Access Confirmation window like the ones below now, you should be able to click ‘Yes’ to continue on each of them
Now you should be able to select a template from the ‘Certificate Template’ drop-down menu. Ensure you select the certificate template that we created previously – ‘SCOM Template’ in this example, and then enter the Fully Qualified Domain Name (FQDN) of the requesting computer into the ‘Name’ field as shown in the screen below
From the same window, scroll down to the end and ensure that the ‘Mark Keys as exportable’ option is selected, choose your key size (or leave at the default of 2048) and then again enter the FQDN of your requesting server into the ‘Friendly Name’ field at the end of the page as below
Once you have entered all of the information required and are happy to proceed, click the ‘Submit’ button at the bottom of the page to finish the request.
You will then see the following ‘Active-X’ and ‘Web Access Confirmation’ alerts which you need to select ‘Yes’ to continue
Finally, you need to click the ‘Install this certificate’ link to install the certificate onto your requesting server
You should see a window like this to confirm the new certificate has been successfully installed....or so you might think!
Although the screen above states that your new certificate has been installed onto your computer, you will find that if you open the ‘Certificates’ MMC snap-in for ‘Certificates (Local Computer)’, there is no sign of your newly created and imported certificate!!!
Thankfully, there is a pretty simple solution to this. The problem occurs because the certificate template creation within Windows Server 2008 doesn’t have provision to specify where exactly the certificate will be stored when you ask it to ‘Install This Certificate’.
It automatically installs the new certificate into the Certificates MMC Snap-In under the ‘Certificates – Current User’ window instead and not the ‘Local Computer’ option as we would like!
All we need to do here is to export this certificate from the ‘Certificates – Current User’ store and import it into the ‘Certificates – Local Computer’ store to enable SCOM to use it for authentication of the computer.
Update: If you open both certificate stores in the same MMC snap-in window, you should be able to just drag and drop the certificate from ‘Certificates – Current User' to ‘Certificates – Local Computer’. This will also retain the private key and should help you avoid the additional steps below using the Certificate Export Wizard.
Simply, right-mouse click on the certificate and select ‘All Tasks’ and then the ‘Export’ option
Now click through the ‘Certificate Export Wizard’ to export the certificate and its private key to a location on your C:\ drive.
You should now be able to see the exported file on the root of your C:\ drive as shown
The next step is to now import this certificate into our ‘Certificates – Local Computer’ store using the Certificates MMC snap-in again
Complete all of the steps in the ‘Certificate Import Wizard’ to bring the certificate into the Local Computer Store
This completes the certificate request using the SCOM Certificate Template and the certificate export-import into your Windows Server 'Local Computer - Certificates' store.
In the final blog post (Part 4) of this series, I will explain how manually install the SCOM agent, update it to the latest Cumulative Update and then how to import the certificate into SCOM to use for authentication when monitoring the SCOM Gateway, untrusted domain/DMZ servers.